1. What are two authentication methods that an access point could use? (Choose two.)
EAP
2. What term describes the encoding of wireless data to prevent intercepted data from being read by a hacker?
encryption
3. A technician has been asked to provide wireless connectivity to the wired Ethernet network of a building. Which three factors affect the number of access points needed? (Choose three.)
the size of the building
the number of solid interior walls in the building
the presence of microwave ovens in several offices
Wireless networks broadcast data over a medium that allows easy access.
5. Which WLAN component is commonly referred to as an STA?
wireless client
6. What type of authentication does an access point use by default?
Open
7. What is the difference between using open authentication and pre-shared keys?
Pre-shared keys require a MAC address programmed into the access point. Open authentication does not require this programming.
8. What are three advantages of wireless over wired technology? (Choose three.)
anytime, anywhere connectivity
easy and inexpensive to install
ease of adding additional devices
9. Which statement is true concerning wireless bridges?
connects two networks with a wireless link
10. Which statement is true concerning an ad-hoc wireless network?
created by connecting wireless clients in a peer-to-peer network
11. Which two statements about a service set identifier (SSID) are true? (Choose two.)
tells a wireless device to which WLAN it belongs
all wireless devices on the same WLAN must have the same SSID
12. What access-point feature allows a network administrator to define what type of data can enter the wireless network?
traffic filtering
13. What are the two WEP key lengths? (Choose two.)
64 bit
128 bit
14. Complete the following sentence: WEP is used to ______ , and EAP is used to _____ wireless networks.
filter traffic; select the operating frequency for
15. Why is IEEE 802.11 wireless technology able to transmit further distances than Bluetooth technology?
has higher power output
16. What are two benefits of wireless networking over wired networking? (Choose two.)
mobility
reduced installation time
17. What does the Wi-Fi logo indicate about a wireless device?
The device is interoperable with other devices of the same standard that also display the Wi-Fi logo.
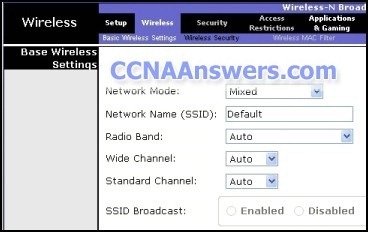
18.
Refer to the graphic. In the Wireless menu option of a Linksys integrated router, what does the Network Mode option Mixed mean?
The router supports 802.11b, 802.11g, and 802.11n devices.
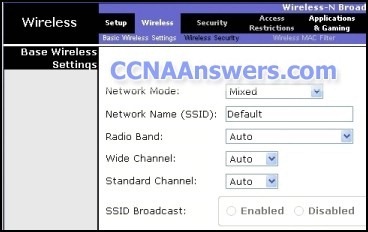
19.
Refer to the graphic. In the Wireless menu of a Linksys integrated router, what configuration option allows the presence of the access point to be known to nearby clients?
SSID Broadcast
20. Which two statements characterize wireless network security? (Choose two.)
With SSID broadcast disabled, an attacker must know the SSID to connect.
Using the default IP address on an access point makes hacking easier.
21. Which statement is true about open authentication when it is enabled on an access point?
requires no authentication



Post Comment
Tidak ada komentar:
Posting Komentar